

We’ve Helped More Than 4 Million Members

Aliesha B.
“Drowning in debt was a nightmare. Credit & Debt was my lifeline. The real hero was my debt coach. She was super helpful and knowledgeable. She broke down my debt into manageable steps and even helped me negotiate with creditors. Now I'm finally on track to becoming debt-free! Highly recommend!”


Corey T.
"Saw ‘Credit & Debt’ in the employee benefits package – thought ‘cool perk.’ Now, it’s a lifesaver! Cleared my student loan debt and finally feel financially secure. Thanks for the unexpected game-changer!"


Emma E.
"Never understood budgeting. Now, with the Credit & Debt app and my amazing debt coach turned into a budgeting pro."

How to Use Strategic Credit Disputes to Improve Client Profiles and Strengthen Client Relationships

Many clients don’t realize their credit report may be inaccurate.
They assume the information on file is correct, and when their score stalls or an approval falls through, they often accept that outcome as final.
Credit report errors are more common than many consumers realize, and they’re rarely obvious.
An incorrect late payment, duplicate account, or collection tied to the wrong person can look like any other line item on a credit report.
For clients who are actively working to rebuild their credit, these inaccuracies can undo months of effort.
That is where credit education professionals have an opportunity to step in. Strategic disputes are not just about correcting mistakes.
They are an opportunity to improve report accuracy, create early momentum in the credit building journey, and build trust through a process clients often find confusing on their own.
This guide explores how strategic disputes can support stronger credit profiles, better client communication, and longer-term loyalty.
Why Credit Reporting Accuracy Matters
Every credit improvement strategy starts with an accurate report.
If the information on file is incorrect, outdated, duplicated, or incomplete, it becomes harder to understand what’s really holding a client back. That impacts everything that comes next, making it harder to provide useful guidance.
Inaccuracies come in many forms:
- Duplicate tradelines
- Incorrect late payments
- Outdated balances
- Accounts that don’t belong to the consumer
- Derogatory items reported incorrectly
When that information is wrong, the client is working from the wrong starting point.
This is where credit professionals create real value. You’re not simply reviewing a report. You are helping clients understand what is accurate, what isn’t, and what deserves action.
That clarity helps clients feel more confident in the process and gives you a better foundation for guiding next steps. The gap between what a client has done and what their credit file shows is your opportunity.
What Makes a Dispute Strategic?
There’s an important caveat to remember: not all disputes are strategic. A reactive dispute happens when a client notices something wrong and submits a complaint.
A strategic dispute is a focused effort to identify where errors exist, assess how they affect your client’s overall profile, and challenge them through the right channels.
Strategic disputes focus on challenges that actually move the needle:
- Outdated negative accounts that should have aged off a report
- Misattributed debts or collections that belong to someone else
- Duplicate collection entries for the same account
- Incorrectly reported late payments
- Accounts that resulted from identity theft or a mixed file
When disputes are handled strategically, they become part of a larger plan. They help clear what should not be there, so the client has a more reliable picture of where they stand.
This also shifts how clients experience the process of working with you. Instead of seeing disputes as a shortcut to better credit, they begin to understand them as one important step in a longer journey.
How Disputes Can Help Strengthen a Client’s Credit Profile
Removing an inaccurate collection or correcting a misreported late payment can meaningfully improve a client’s credit score, sometimes enough to move them into a stronger lending tier.
A cleaner profile also tells a more credible story to lenders, which can influence decisions beyond the score itself.
For clients working toward a specific goal, such as buying a home or securing a loan for a new business, these corrections can be the difference between approval and denial.
This can also help create early momentum that helps clients remain engaged and follow through on next steps. Disputes are rarely the full story, but they can open the door to better habits.
When credit professionals treat disputes as an important part of a broader credit strategy, they create a stronger client experience and a stronger business model.
Long-term client progress usually comes from a mix of accurate reporting, a pattern of better credit habits, positive tradelines, and real insight into what’s changing over time.
Best Practices for Helping Clients Navigate Disputes
The dispute process can be confusing and frustrating for clients who aren’t familiar with it. A credit professional’s job is to demystify it and manage it on their client’s behalf.
A few guiding principles can make all the difference:
- Document everything: Every dispute should be supported by clear evidence, such as account statements, correspondence, or identity verification. Thorough documentation can significantly improve the odds of a successful outcome.
- Communicate clearly and often: Keep clients informed at every stage of the process. Explain what was disputed, why, what to expect, and what the outcome was. Clients who understand the process will trust it, and by extension, trust you.
- Set realistic expectations: Not every dispute will succeed, and not every inaccuracy will lead to a dramatic score increase when removed.
- Honest guidance preserves credibility and prevents disappointment.
- Keep clients on a timeline: Under the Fair Credit Reporting Act, credit bureaus have 30 to 45 days to investigate disputes.
- Understanding timelines, and managing client expectations around them, further positions you as an invaluable resource.
- Follow up: Disputes can stall or remain unresolved. Following up ensures the outcome actually appears correctly on your client’s report.
Turning Client Support into Long-Term Loyalty
Clients don’t stay simply because of a service; they stay because of how that service made them feel.
When you help clients handle disputes with skill, clear communication, and genuine care for the outcome, the client walks away with more than an improved credit score. They walk away feeling supported and understood.
That feeling is what generates referrals and turns a one-time engagement into an ongoing advisory relationship.
Credit professionals who expand beyond dispute rounds consistently see longer client lifecycles and stronger retention.
Client relationships shouldn’t end when the dispute phase does. With the right tools in place, they can continue through every stage of a client’s financial journey.
That isn’t just better for the client, it’s better for your business.
Related: Protecting Your Clients in the Age of Evolving Fraud: Key Trends and Predictions
What You Can Deliver Through IDIQ
Dispute management and proactive monitoring only work as loyalty tools if they are easy to deliver consistently.
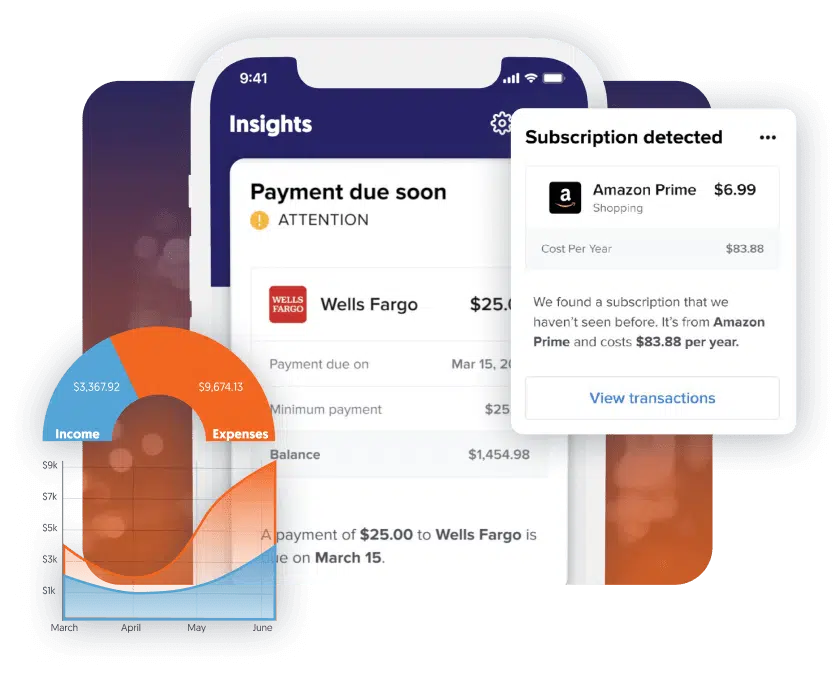
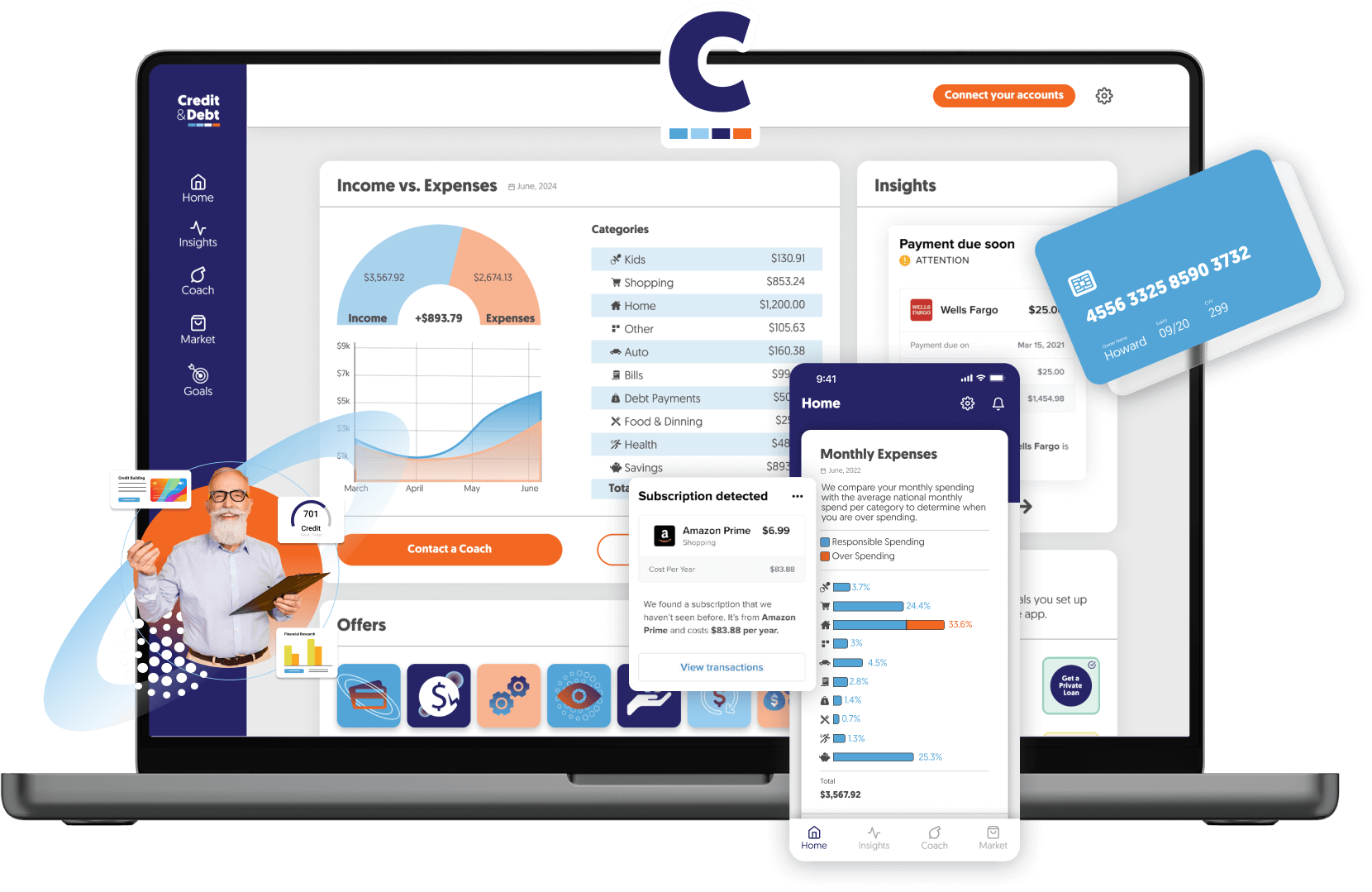
With the full IDIQ product suite, you can give your clients access to:
- Credit monitoring and reports, with real-time alerts that flag changes and errors as soon as they appear
- ScoreCasterIQ, to help clients simulate the impact of potential changes and stay motivated throughout the process
- CreditScoreIQ, a DIY platform that keeps leads and clients engaged
- Rent reporting and utility reporting, to help clients add positive payment history and build momentum alongside the dispute process
- Identity theft protection, including $1 million in identity theft insurance, so clients are covered if an error turns out to be something more serious
Those who combine IDIQ partner solutions consistently earn more per client, extend their customer lifecycle, and build the kind of recurring revenue that makes a practice resilient.
Disputes close, but relationships don't have to.
When clients can see their progress in real time, disputes are proof that the process is working.
That confidence is what keeps clients engaged - and engaged clients are the foundation of a practice that grows.
Interested in becoming an IDIQ partner? Get started today.
AB 2747 Compliance and Rent Reporting: How to Avoid Building In-House Solutions

California property management companies face a new operational reality.
Effective July 1, 2025, California Assembly Bill 2747 requires property owners and managers of multifamily communities to offer residents the option to report their on-time rent payments to a major credit bureau.
At a high level, the law is easy enough to understand; the harder part is building a repeatable process around it.
For property management companies, the challenge comes in implementation. Teams already managing a long list of responsibilities must determine how to implement this additional process in a compliant, efficient, and realistic way.
That means managing annual notices, resident elections, signature collection, bureau reporting responsibilities, and onsite support across multiple properties and lease cycles.
For many property management companies, AB 2747 is less a policy question than a workflow question: how do you support compliance without creating a new burden for teams?
In this guide, you’ll learn:
- Why AB 2747 is creating new pressure for property management companies
- What the law requires
- Where implementation tends to get complicated
- How a turnkey model can make compliance easier to manage
AB 2747: What Property Management Companies Need to Know
AB 2747 requires property owners and managers with 16 units or more to offer residents the option to report on-time rent payments to at least one major credit bureau, including Experian, Equifax, or TransUnion.
Participation is optional - residents can choose whether or not to take part.
Property managers are responsible for making sure any rent data that is reported is accurate and submitted on time.
For new leases entered on or after April 1, 2025, the offer must be made at signing and then at least once every year following.
For existing leases, the offer must be made by April 1, 2025, then annually moving forward.
In other words, AB 2747 is not a one-time communication requirement. It creates an ongoing process that property management companies need to be prepared to manage consistently.
Why AB 2747 Gets More Complicated in Practice
The communication requirements matter just as much as the reporting requirements.
Notices must include specific required information, and they can be sent by email or first-class mail.
If an email is not successfully sent and the notice is sent by mail, the landlord must include a self-addressed, stamped envelope so residents can return the election form.
While these requirements sound straightforward, it requires a process that has to work across multiple properties, residents, staff members, and systems.
This is where the operational burden starts to creep in. Non-compliance can create regulatory risk, but it can also create additional friction for property teams and residents alike.
Why Property Management Companies Hesitate to Manage Rent Reporting Internally
For many property managers, the question isn’t whether or not it’s worth it to provide rent reporting to their residents. The harder questions are the ones that follow:
- Do we have bandwidth for this?
- Who can manage the communication around it?
- How do we track resident elections accurately?
- What happens if notices fail to deliver?
- Who handles reporting responsibilities?
- How much extra work does this create?
At the same time, many property management companies recognize that rent reporting can support resident financial wellness, and strengthen the overall resident experience - especially when the program is managed well.
When rent reporting feels like just another compliance program layered onto property operations, even organizations that are interested in it may stall.
And it’s not because they don’t see the value - it’s that they only see the workload attached to it.
The Workflow Gaps That Make AB 2747 Harder to Manage Internally
On paper, AB 2747 looks like a simple resident benefit: give renters the option to have on-time payments reported. But when you try to run it across multiple properties, lease start dates, and communication channels, the work quickly breaks into a series of operational gaps that most teams are not staffed or tooled to manage consistently.
Annual Compliance Notifications
AB 2747 creates an ongoing obligation to offer rent reporting at the right times and in the right way. That means notices need to be generated, delivered, and documented consistently across lease cycles and properties.
Without a standardized process, that can quickly turn into another manual workflow for teams that are already stretched thin.
When that process depends on internal tracking, consistency becomes harder to maintain, especially as properties and lease activities scale.
Resident Communication Gaps
While a quick email can work for many residents, it is not a one-size-fits-all solution. Some residents may not have an email address on file. Some residents may miss or misunderstand the notice. As those exceptions start piling up, compliance becomes much harder to manage at scale.
And when first-class mail is the fallback, that means cost and coordination need an increase. This is one of the first places where a simple compliance requirement starts to turn into a heavier operational process.
Enrollment Tracking Gets Complex Quickly
Rent reporting may sound straightforward, but understanding who received the offer, who enrolled, what they agreed to, and how that information is stored and maintained can be complicated.
When multiple communities are involved, it can quickly become a messy administrative issue without proper structure in place.
Consent Collection and Record Keeping After
A rent reporting offer is not just for awareness; it requires written election with specific pieces of information. That means property management companies need a dependable way to collect, store, and retrieve consent records.
Precise record keeping is key when teams need to verify tenant elections, answer their questions, or document compliance down the line.
Bureau Reporting Introduces Risk
Many property management companies are hesitant to take on the responsibility of sending data to credit bureaus, as they are not typically data furnishers or aggregators and often lack in-house expertise in reporting standards, data reconciliation, reporting timelines, and dispute resolution.
As a result, many are reluctant to build and manage these internal processes on their own.
Onsite Teams Need Support
Even if the corporate team owns the decision, onsite teams are the ones feeling the impact first. They’re the ones fielding resident questions, handling confusion around enrollment, or managing follow-up about how the program works.
If they do not have clear guidance, the program can create more friction at the property level than expected.
This is why education and support are just as critical as the reporting mechanics themselves.
A workable model should do more than ensure compliance - it should also prevent on-site teams from being burdened with unnecessary processes while providing residents with a clear and straightforward experience.
A Practical Rent Reporting Solution Can Help
Property management companies need a model that makes compliance easier to execute in practice.
A practical rent reporting solution should support:
- Resident notifications
- Consent capture
- Election tracking and record keeping
- Accurate bureau reporting
- Resident support
- Seamless integration with existing property management systems if possible
Most importantly, it should reduce manual workload for both corporate and on-site teams, rather than simply serving as a compliance checkbox.
How IDIQ Helps Reduce the Lift
IDIQ helps property management companies simplify the process. With a turnkey rent reporting solution designed to support AB 2747 implementation, IDIQ reduces the amount of process-building property management companies have to take on internally.
IDIQ manages the parts of the process that many companies do not want to own internally, including:
- Resident enrollment
- Credit bureau reporting
- Ongoing customer support
To make implementation easier, IDIQ supports integration with major property management systems, helping reduce friction during rollout.
Instead of asking property teams to build a reporting operation from scratch, IDIQ gives them a more practical path to launch and sustain rent reporting with less internal strain.
Important Program Note: Direct Opt-In vs. Lease Enroll
Program structure matters as it has a direct impact on workload, adoption, and long-term sustainability.
For property managers offering rent reporting as a direct opt-in program, IDIQ charges an annual platform fee to support program sustainability. This is because direct opt-in programs require significant effort, including onboarding, data management and reconciliation, and ongoing resident support.
Property management companies that launch rent reporting through lease enroll with opt-out participation do not need to pay an annual platform fee. Adoption rates for an opt-out system are in the 80 to 90% range, meaning the program is generally more efficient to support operationally.
This is an important distinction for property managers to evaluate how to roll out rent reporting. The structure of the program does not just affect participation; it affects total lift, cost, and long-term sustainability.
Final Notes
Annual notices, reporting responsibilities, and ongoing education can turn rental payment reporting into a much heavier lift than property management companies might initially expect.
That is why implementation matters so much. The best rent reporting programs are compliant on paper, of course, but they are built to work in practice without overly burdening the teams responsible for carrying them out.
IDIQ helps property management companies support AB 2747 compliance without taking on all of the operational burden themselves.
Want to simplify your rent payment reporting and ensure compliance? Partner with IDIQ today!
How to Scale Your Business by Partnering with Mortgage Lenders and Realtors

Key Takeaways from a live webinar with Tiffany Cross, IDIQ VP of Sales
Many credit businesses try to grow by getting louder, with more posts, more outreach, and more consumer marketing.
But the most sustainable growth comes from something quieter - trusted referral relationships with mortgage lenders and realtors.
In a recent IDIQ partner webinar, Tiffany Cross, IDIQ’s VP of Sales, broke down what consistently drives strong referral partnerships.
The foundation is simple: lead with ethics and compliance, learn how to speak the language of lenders, and design your services around a loan officer’s workflow so you become easy to trust and easy to refer.
Her message is consistent: lender partnerships are not won by being louder. They are won by being trustworthy, compliant, and easy to work with.
The trust-building foundation starts with two non-negotiables:
- Lead with an authentic “why” that explains what drives you and why you operate differently.
- Operate with ethics and compliance, not flashy marketing.
Mortgage professionals evaluate risk. They’re deciding whether a credit partner is safe to plug into their process, and whether that guidance will create fewer surprises later in the transaction.
And they’re considering everything: your website, your pricing, even your social media presence. If what they find signals credibility, you become referable.
Below, you’ll find a recap of the actionable insights from the webinar, covering:
- What lenders look for before they refer to credit partners
- How to position your “why” as credibility
- The questions that reveal partnership fit
- How to communicate like a lender
- How to quantify opportunity using the “denial pool”
- How to stay top-of-mind with education lenders can reuse
- How IDIQ tools support your workflow and credibility with mortgage partners
Defining What Sets You Apart Through Partnership Onboarding
Your differentiation play is not marketing. It is partnership onboarding.
Treat early conversations with lenders and realtors like working sessions, not sales calls. Your goal is to map their workflow, then shape your services around their process so you become easy to plug in.
Aim for a 70/30 split - let the lender talk most of the time. Then get specific on the operational details that determine whether you become easy to refer: What does “good” look like in this partnership?
- Where do you source your clients?
- How do you prefer updates: monthly or weekly, email or text?
- How often do you re-pull credit, and what do you need between pulls?
- What causes the most fallout in your pipeline: score, DTI, utilization, disputes, thin files?
- How many credit reports do you pull each month, and how many are denied? Why?
Follow this simple, three-step foundation
- Articulate your story
- Dive deeply into what matters to lenders
- Identify how that translates into greater loan conversion
This is what sets you apart. Not a tagline, but an aligned process they can trust with their clients.
Identifying Your Ideal Demographic
Before you invest in outreach, get specific about who you serve best.
Start by defining your ideal client and the segments most likely to engage and benefit from your services.
Then mirror that when you approach mortgage lenders in your market. Look for lenders and realtors who consistently work with that same borrower profile and loan programs.
When you align with professionals serving the same borrower profile, the partnership works better for everyone. You become a clean extension of the lender’s workflow, the borrower gets a seamless experience, and the lender is more likely to refer you.
Also, match your message to the audience. Co-brandable flyers, open house leave-behinds, and borrower-specific education can make it easier for lenders and realtors to talk about your services in a way that feels helpful, not salesy.
To find aligned partners faster, plug into the same local environments they rely on, such as local real estate associations and professional networks. This keeps your outreach focused, builds credibility through proximity, and helps you stay visible with the right people.
Speak the Language of a Lender: Takeaways for Credit Education Professionals
Strong lender partnerships start with understanding what lenders are actually optimizing for. The goal is not just to “improve credit.” It’s to help the lender move more borrowers from “denied” to “approved” with fewer surprises during the process.
Your job is to reduce friction in the pipeline and make borrower progress easy to track.
Ask questions that map to lender workflow:
- The loan amounts they typically fund
- The borrower profiles they target
- How they source leads and what the process looks like operationally
- Which loan programs they offer
- The minimum FICO requirements they use for approval and better pricing
- How often they re-pull credit and what updates they want from you between pulls
- What underwriting factors most commonly hold deals back in their pipeline (DTI, utilization, disputed accounts, thin files)
- What their ideal update looks like (format, frequency, and the types of data that matter to them)
Align reporting to mortgage scoring
Just as important: make sure you’re talking about scores the way mortgage teams do. Lenders commonly evaluate borrowers using specific mortgage FICO models like FICO 2, 4, and 5, not the consumer scores borrowers see in free apps. That’s why score updates can break trust if they’re not aligned.
Coach for underwriting realities, not just score movement
Don’t treat mortgage readiness as a score-only project. Underwriting guidelines can supersede score improvements or work alongside them.
For example, debt-to-income (DTI) is one of the top qualifying factors that lenders look at to determine if a buyer is mortgage-ready.
As a credit expert, you may not be able to help your client pay down debt, but you should understand what good DTI looks like.
And in the meantime, you can coach your clients on removing derogatory information, building positive tradeline history, and reducing credit card utilization ratios.
Use a Lender’s Denial Pool to Create Opportunity
To partner effectively with mortgage lenders, it helps to understand what happens before a borrower becomes a referral.
In many cases, a loan officer starts with an in-depth intake conversation and a soft credit pull to gauge readiness.
If a borrower falls below a lender’s workable threshold, the loan officer may run internal scenario tools that simulate quick win actions, often centered on paying down credit card debt.
These tools can be useful for borrowers who are close, but they can be limited when utilization changes alone may not be enough to move someone from the low 500s into an approvable range.
This is the gap credit education professionals can fill.
Ask lenders how many applications they denied last year and what those denial scenarios looked like, then clarify how many denied borrowers were simply below the lender’s target score range versus facing issues like DTI, thin credit, or affordability.
That denial pool reveals your biggest opportunity and most lenders are not chasing perfect credit.
They just need borrowers to move from the high 500s into the 620 to 640 range where funding and pricing get easier. Once you know how many borrowers sit below that band, you can design a repeatable referral pathway.
Offer free consultations for denied applicants, and invite the lender to join when appropriate.
That way the lender can see exactly how you evaluate a credit report, how you communicate with your clients, and how you translate the plan into mortgage-ready next steps.
Rent reporting and utility reporting can be a big help for customers who don't have much credit history yet, giving lenders more information about how reliably they pay their bills.
These payments don't count toward mortgage credit scores right now, but they still matter. Here's why:
- They add new accounts to a customer's credit report, which shows a track record of on-time payments
- Other lenders, like credit card companies, do use these scores, making it easier for customers to get approved
- As they open and manage those new accounts responsibly, their overall credit profile gets stronger
- Over time, stronger profile can affect the scores used in home buying decisions
The other thing worth knowing is that credit scoring is always changing. Lenders are starting to look at more types of payment history than they used to.
Helping your customers build this record now means they'll be in a better position when those changes happen.
Build a Two-Track Pathway So Leads Don’t Disappear
As you work through free consultations, you may find not every borrower who needs help is in a position to work with you - at least right away.
Rather than letting those leads drop, build a two-track funnel:
- A full program for borrowers who are a fit and can start your program now
- A lower-cost DIY path for those who need support but can’t commit yet
Or a combination of both. A hybrid model that combines full-service credit support with DIY tools. This approach offers flexibility and may better align with a broader range of client needs.
Keep the DIY clients on an education drip with periodic check-ins so they can move into your full program when the time is right.
Add a win-win lenders can offer at closing
You can also utilize a strategy that helps lenders lean in and helps borrowers feel supported: a closing cost credit.
When a borrower graduates from your program and closes with the referring lender, the lender offers a credit at closing that reimburses part of the borrower’s cost for your services.
It creates a clean incentive for the borrower to stay with the lender who referred them, and gives the lender an easy way to reinforce the partnership at the finish line.
Show the Math: The Revenue Hiding in “Not Yet”
If you want a lender to truly buy in, build them a business case. Put numbers to the borrowers they’re turning away, and show them what even a small conversion lift could be worth.
Ask for:
- How many applicants they deny in a year
- Their average loan amount
- Whether they buy leads, and what their lead cost looks like
Then run a simple scenario.
If a lender declines 100 borrowers annually and the average loan is $300,000, that is $30,000,000 in “not yet” volume. If your partnership helps them convert a portion of that denied pool over time, that’s additional funded volume they can tie back to a repeatable workflow
The point is that “not yet” is expensive for lenders.
Many are paying for leads and pulling credit only to deliver a no. When you help convert even a portion of that denied pool, you’re not just supporting borrowers. You’re helping lenders recover value from spend they’re already making.
Staying Top-of-Mind with Mortgage Pros: Build Education They Can Use
Once you understand a lender’s workflow and your role in it, the next challenge is staying front and center. To become their go-to credit expert, create credit education that is relevant to them and give them tools they can co-brand and share.
Educate without selling
Education sessions should not turn into a pitch. If you walk into a lunch-and-learn and start selling, you likely won’t be asked back. The better approach is to reverse engineer what helps their business close more deals and deliver that value directly, in a way that feels practical and respectful of their time.
Topics lenders and realtors can reuse
There are a range of topics that are well-suited to quick 30-minute sessions. Consider:
- The difference between FICO and VantageScore and how models differ
- How models react to different factors and why that matters in borrower conversations
- What good utilization looks like and credit card do’s and don’ts
- The difference between hard and soft inquiries
- The basics of alternative credit for thin-file borrowers, including rent reporting and utility reporting
- Changes in the credit space, including newer models that use trended data
- How installment debt vs revolving debt impacts readiness
Create a cadence
Avoid giving everything all at once. Instead, offer strong “nuggets” on a consistent cadence so partners want you back quarterly or monthly. Being the person who drops in regularly to deliver relevant education keeps you visible.
Build a co-brandable content library to feed your funnel
Beyond live sessions, build a library of resources that partners can distribute. Provide content they can email through their CRM, share with borrowers, repurpose in workshops, or post through their own channels.
Lenders want easy access to credit information and strategies they don’t have to hunt for. When you become their go-to resource, they start bringing you scenarios before they even refer the borrower, and you can respond with both guidance and a piece of education that supports it.
Industry Visibility
Local visibility matters, too. By attending events, joining real estate communities, and building relationships, you can expand your reach.
Building Strong Partnerships with Real Expectations and Clear Boundaries
Trust grows when expectations stay realistic. Set mutual goals for what referred clients should receive in your program, and avoid making any promises you can’t keep.
You also need the ability to say no. For example, if a lender needs a borrower to close in 15 to 30 days, but their credit report shows major credit card debt, unpaid collections, and fresh late payments, the response is simple: you can help, but not on that timeline.
The right boundaries protect the relationship and position you as the partner who tells the truth early.
Final Thoughts
Throughout the webinar, the message was consistent: the strongest mortgage referral partnerships are built on providing value.
Learn the language of lenders. Understand their workflow. Communicate the way they prefer. Coach for underwriting realities, not just score movement. Build pathways for borrowers who cannot enroll immediately. Show the math. And finally, protect relationships with realistic expectations and clear boundaries.
When all of these elements come together, lenders gain a reliable process for turning “not yet” into “approved,” and credit education professionals gain a repeatable partnership engine.
Want to keep building on these strategies? IDIQ hosts monthly webinars on the third Thursday of every month, built specifically for credit education partners who want to scale their business, improve operational workflows, and drive more revenue.
What New Legislation AB 2747 Means for Property Managers

As of September 19, 2024, AB 2747 is officially in effect, requiring property managers to take prompt steps to remain compliant.
California Assembly Bill 2747 (AB 2747) introduces new requirements for rent payment reporting that directly affect property managers across the state. Understanding how this law works and how to implement it correctly is essential for maintaining compliance, supporting residents, and avoiding unnecessary operational risk.
This article explains what AB 2747 requires, key compliance deadlines, and how partnering with IDIQ can simplify rent payment reporting while creating additional value for property managers.
Key Takeaways
- AB 2747 requires property managers of buildings with 16 or more units to report positive rent payments to credit bureaus, helping residents build credit.
- Property managers must establish accurate, secure reporting systems, and notify residents by the deadlines.
- IDIQ offers integrated rent payment reporting solutions, ongoing support, and marketing materials to help property managers comply efficiently while also creating ancillary income opportunities.
What is AB 2747?
California Assembly Bill 2747 (AB 2747) expands access to rent payment reporting for California residents. Under this law, property managers of buildings with 16 or more units must offer positive rent payment reporting to credit bureaus.
When residents’ on-time rent payments are reported, those payments can appear on their credit reports, helping them establish or improve their credit scores.
AB 2747 builds on earlier legislation such as California Senate Bill 1157 (SB 1157). While SB 1157 applied to a narrower group of properties, AB 2747 significantly broadens eligibility, allowing more residents to benefit from credit-visible rent history and promoting greater financial inclusion statewide.
AB 2747 officially passed on September 19, 2024. Property managers should be preparing now to meet compliance requirements.
Key deadlines to know:
- Leases entered into on or after April 1, 2025
The offer of positive rent payment reporting must be made at lease signing and at least once annually thereafter. - Leases active as of January 1, 2025
The reporting offer must be made no later than April 1, 2025, and at least once annually thereafter. - Offers may be delivered by email or mail.
Compliance Requirements Under AB 2747
To comply with AB 2747, property managers must report positive rent payments for qualifying properties.
This includes the obligation to:
- Report rent payments: Submit residents’ positive rental payment history to credit bureaus
- Provide resident notification: Inform residents about rent payment reporting and explain how it may affect their credit.
- Ensure accuracy: Maintain precise records to prevent errors or disputes.
- Follow state reporting guidelines: Adhere to required formats, frequencies, and compliance standards.
Implementing Rent Payment Reporting Systems
Rent payment reporting can be complex, but the right systems make it manageable.
Related: AB 2747 Compliance and Rent Reporting: How to Avoid Building In-House Solutions
Best practices for implementation
Assess Your Current Systems:
- Review existing property management and accounting software.
- Identify gaps or upgrades needed to support compliant reporting.
Select a Rent payment reporting Partner:
- Choose a provider that integrates with your existing systems.
- Ensure reporting to all three major credit bureaus.
Implement and Train:
- Work with your provider to ensure a smooth rollout.
- Train staff on new workflows to maintain accuracy and consistency.
Communicate With Residents:
- Clearly explain how rent payment reporting works and why it benefits them.
- Provide guidance on how residents can ensure their payments are reported correctly.
💡 Want help offering rent payment reporting to your residents?
👉 Partner with IDIQ today
How IDIQ Helps Property Managers Stay Compliant
IDIQ provides turnkey rent payment reporting solutions designed to support AB 2747 compliance.
By partnering with IDIQ, property managers gain access to tools and expertise that reduce operational burden while enhancing resident outcomes.
Benefits of Rent Payment Reporting
Rent payment reporting isn’t just a compliance requirement—it delivers meaningful benefits across the board.
Benefits of Property Managers:
- Encourages on-time payments by giving residents a credit incentive.
- Reduces tenant turnover through higher satisfaction and retention.
- Enhance trust by supporting residents’ financial well-being.
⭐️ Ready to stay compliant and simplify rent payment reporting ?
👉 Partner with IDIQ today
Benefits for Residents:
- Builds credit through rent they already pay.
- Improves access to loans, credit cards, and financial opportunities.
Industry-Wide Benefits:
- Positions property managers as forward-thinking and resident focused.
- Helps organizations stay ahead of evolving legislative requirements.

Setting Up Rent Payment Reporting
Setting up rent payment reporting can seem daunting, especially without the right tools and support. Here’s a brief overview of the basics and the challenges you might face when trying to accomplish this on your own.
Understanding the Basics:
To begin with, rent payment reporting involves regularly tracking and reporting your residents' rent payments to credit bureaus.
This process requires:
- Accurate Payment Tracking: Ensuring that all rent payments are recorded accurately and on time.
- Data Security: Protecting residents' personal and payment information in compliance with data protection regulations.
- Regular Reporting: Submitting accurate and timely reports to all three major credit bureaus to reflect residents' rent payment history.
Challenges of Setting Up Rent Payment Reporting Independently:
- Technical Integration: Integrating a rent reporting system with your existing property management software can be complex and time-consuming. Ensuring compatibility and seamless data transfer is critical but often challenging.
- Regulatory Compliance: Staying compliant with AB 2747 and other relevant legislation requires staying up-to-date with changing regulations and implementing necessary adjustments. This can be overwhelming without expert guidance.
- Resource Allocation: Implementing a new system requires dedicated time, effort, and financial resources. For property managers already stretched thin, this can be a significant hurdle.
- Data Accuracy: Maintaining accurate records and ensuring no discrepancies in reporting is essential. Any errors can negatively impact residents’ credit scores and lead to disputes.
- Tenant Communication: Effectively communicating the benefits and processes of rent reporting to residents is crucial for their satisfaction.
Partnering with IDIQ streamlines AB 2747 compliance while unlocking additional operational and financial value.
With IDIQ, you get:
- Deep expertise in rent payment reporting solutions
- Continuous implementation and operational support
- High revenue-share opportunities or cost-offset options for residents
- Seamless integration with major accounting and property management platforms
- Ready-to-use marketing materials to drive resident adoption
Bottom Line
AB 2747 represents a major shift in how rent payments are reported in California. Property managers who act early can improve compliance readiness, enhance resident satisfaction, and reduce long-term operational risk.
Implementing rent payment reporting on your own can be challenging, but partnering with IDIQ makes it simple, accurate, and efficient
IDIQ rent payment reporting services integrate seamlessly with existing systems, helping you stay compliant while maximizing value for both your properties and your residents.
👉 Partner with IDIQ today to prepare for AB 2747 with confidence.
Resources: